How Can I Effectively Utilize Command Line Interface (CLI) Tools to Enhance My Tactical Operations?
In the realm of tactical operations, the Command Line Interface (CLI) emerges as a powerful tool, empowering users with the ability to wield the full capabilities of their systems with precision and efficiency. This article delves into the significance of CLI tools in tactical scenarios, exploring their advantages and showcasing their diverse applications in reconnaissance, situational awareness, network analysis, and data manipulation.
Essential CLI Tools For Tactical Operations
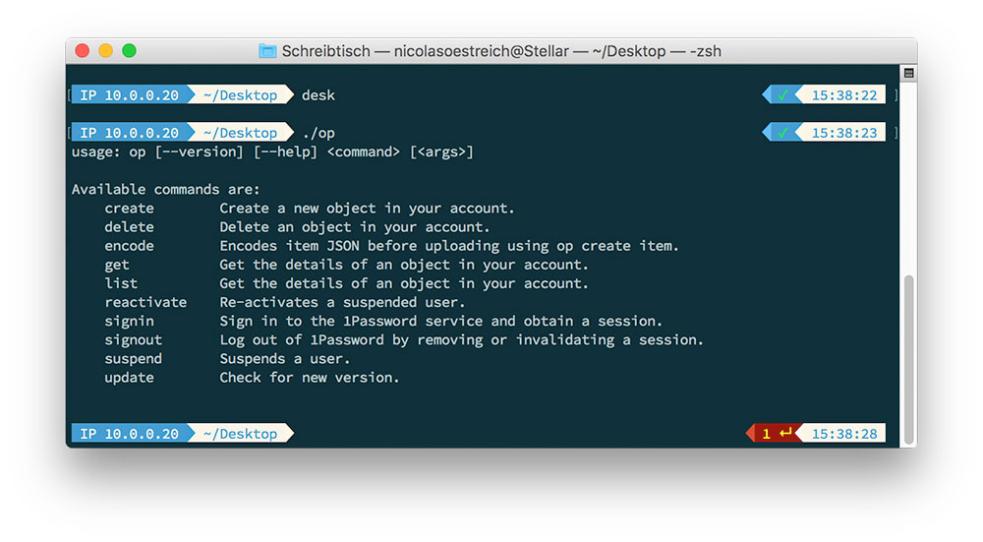
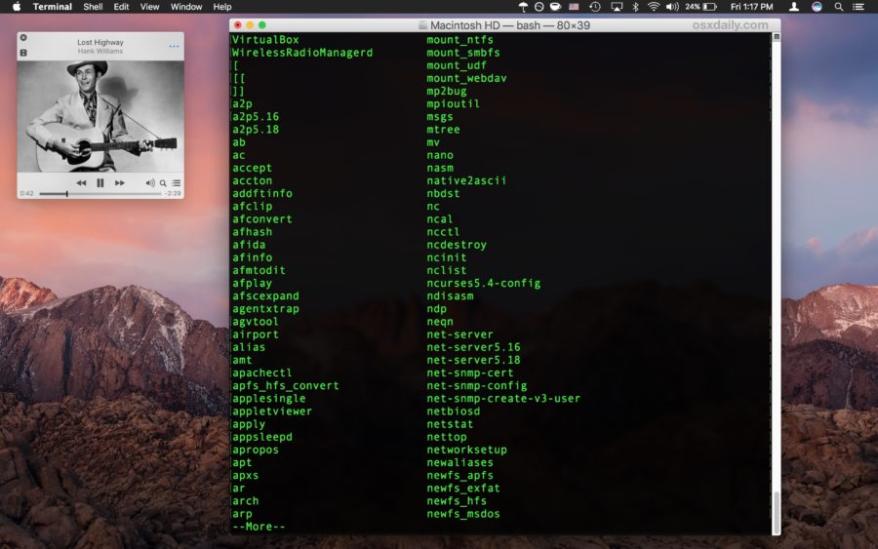
A plethora of CLI tools are available, each tailored to specific tasks within tactical operations. Among the most commonly employed are:
- Reconnaissance and Intelligence Gathering: Tools like Nmap, Wireshark, and Metasploit aid in scanning networks, discovering vulnerabilities, and analyzing network traffic, providing valuable intelligence for informed decision-making.
- Situational Awareness and Decision-Making: Tools like Google Earth, GPSd, and Tactical Analysis Tools (TAT) enable the visualization of data, creation of maps, and tracking of assets, enhancing situational awareness and supporting effective decision-making.
- Network Analysis and Security: Tools like tcpdump, Snort, and Security Onion facilitate the analysis of network traffic, detection of anomalies, and identification of security threats, ensuring the integrity of tactical networks.
- Data Manipulation and Automation: Tools like grep, sed, and awk empower users to parse, filter, and transform data efficiently, while scripting languages like Python and Bash enable the automation of repetitive tasks, streamlining tactical operations.
Reconnaissance And Intelligence Gathering
CLI tools play a pivotal role in gathering intelligence and conducting reconnaissance. Network scanning tools like Nmap and Angry IP Scanner uncover open ports and services, revealing potential vulnerabilities. Tools like Wireshark and tcpdump capture and analyze network traffic, providing insights into network activity and identifying suspicious patterns. Metasploit, a powerful penetration testing framework, enables the exploitation of vulnerabilities to gain access to systems and extract valuable information.
Situational Awareness And Decision-Making
CLI tools enhance situational awareness by providing real-time data visualization and analysis. Tools like Google Earth and GPSd allow users to visualize geospatial data, overlaying tactical information onto maps for better understanding of the operational environment. Tactical Analysis Tools (TAT) enable the creation of complex visualizations, facilitating the analysis of large datasets and supporting informed decision-making.
Network Analysis And Security
CLI tools are indispensable for analyzing network traffic, detecting anomalies, and identifying security threats. Tools like tcpdump and Snort capture and analyze network packets, enabling the detection of suspicious activity and potential attacks. Security Onion, a comprehensive security monitoring platform, integrates multiple open-source tools to provide real-time threat detection and analysis, safeguarding tactical networks from cyber threats.
Data Manipulation And Automation
Data manipulation and automation are crucial in tactical operations. CLI tools like grep, sed, and awk enable the efficient parsing, filtering, and transformation of data, extracting meaningful insights from large datasets. Scripting languages like Python and Bash allow users to automate repetitive tasks, streamlining operations and freeing up valuable time for mission-critical activities.
Case Studies And Real-World Examples
Numerous real-world examples showcase the successful employment of CLI tools in tactical operations. In 2016, the U.S. military utilized CLI tools to analyze network traffic and identify malicious activity during a cyberattack, preventing a potential breach of sensitive data. In 2018, law enforcement agencies used CLI tools to track down a group of cybercriminals involved in a large-scale phishing scam, leading to their arrest and prosecution.
Best Practices And Considerations
Effectively utilizing CLI tools in tactical operations requires adherence to best practices and careful consideration of various factors. Security is paramount, with measures such as strong passwords, regular updates, and network segmentation essential for protecting systems from unauthorized access. Training is crucial to ensure that personnel are proficient in using CLI tools and understand their capabilities and limitations. Integration with existing systems is also important, ensuring seamless interoperability and maximizing the value of CLI tools within the tactical environment.
CLI tools are invaluable assets in tactical operations, empowering users with the ability to harness the full capabilities of their systems and enhance their operational effectiveness. By mastering these tools, tactical teams can gain a decisive edge in reconnaissance, situational awareness, network analysis, and data manipulation, enabling them to make informed decisions, respond swiftly to threats, and achieve mission success.
YesNo

Leave a Reply